Special protection for Critical Infrastructures in times of war
The topic of cybersecurity is gaining renewed importance, especially in the context of the Ukraine war. Critical Infrastructures are particularly important areas that need to be protected. Attacks on these can be very expensive, so it is worth investing in protecting them even in times of peace. The following blog post takes a closer look at the topic of Critical Infrastructures and highlights current problems.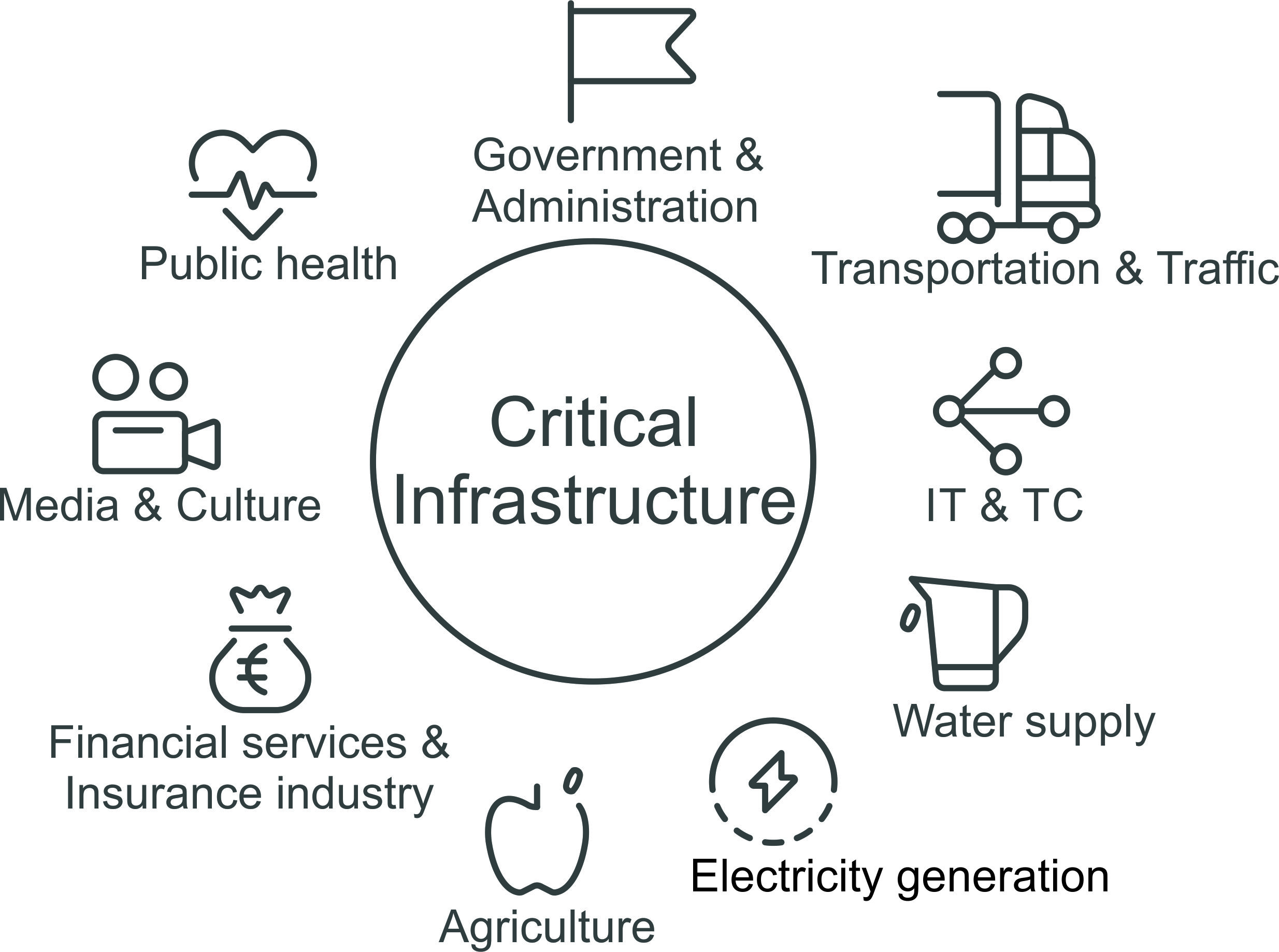
Critical Infrastructures are organizations or facilities with significant importance to the state community. For example, energy and water supply, transportation, as well as medical care and telecommunications fall under Critical Infrastructure. All of these provide us with essentials such as water, electricity and food. They form the basis of life, without which society would not function. The BBK (Federal Office of Civil Protection and Disaster Assistance) is responsible for protection, and its goal is to ensure that the population is supplied as well as possible.
Critical Infrastrucutres in times of war
In addition to global challenges such as climate change, the current Ukraine war poses a major problem for Critical Infrastructures due to the negative changes in the field of international security. In addition to terrorist attacks, there are threats that originate from cyberspace. For example, hacker attacks on the power grid can paralyze the power supply over a large area. In addition, growing digitization increases the interdependence between the Critical Infrastructures, which leads to an even larger attack surface. This makes it all the more important to protect the Critical Infrastructures from attacks by strengthening cybersecurity, primarily through the state.
The main problem with protective measures
The main problem with protecting Critical Infrastructures is that the law on mandatory IT security measures only covers cities with more than 500,000 inhabitants. Cities like Aachen, Augsburg, Münster and many others could be without water, electricity and food in case of cyber attacks on Critical Infrastructure. Thus, the protections are primarily beneficial to large cities; all smaller cities are not necessarily protected from the dangers of cyberattacks on supply chains by this loophole.
Is investing in IT protection worth it on a cost level?
Investments in IT protection are of considerable importance because the consequences of an attack on the Critical Infrastructures also entail fatal cost consequences. In the Anhalt-Bitterfeld district, for example, hackers broke into computers belonging to the authorities' IT systems, allowing secret data to be spied out and manipulated. The ransom demand amounted to a substantial € 500,000. 160 specialized procedures were affected and were not fully functional for about 1 year. Thus, the lack of IT protection ended up costing over € 2 million, the payment of which could have been avoided by prior investment in IT protection.
As digitization continues to grow, the increasing demands on the security of processes and systems must also be recognized and implemented. This makes it all the more important to prepare in times of peace for hacker attacks during a wartime event and take measures to protect against them.
30.09.2020 - Online events – more than a room [more...]
28.08.2020 - Consent-free tracking with Matomo as an alternative to Google Analytics [more...]
22.07.2020 - Privacy Shield Judgement - Privacy vs mass surveillance [more...]
17.06.2020 - Data protection-compliant work from home: decentralized and open source [more...]
26.05.2020 - GDPR-compliant e-learning with BigBlueButton, Moodle and Nextcloud - data protection begins with the little ones [more...]
24.04.2020 - [more...]
20.04.2020 - Home office tools: not everything that glitters is gold ... [more...]
18.03.2020 - Home office at the time of the corona pandemic [more...]
07.11.2019 - Judgment of the ECJ on (tracking) cookies [more...]
24.10.2019 - Environmental protection by aixzellent [more...]
